The unanticipated expansion of the World Wide Web has, in some respects, transformed the entire planet into a single cyber hamlet. However, new dangers emerged as the world transitioned from a physical to a digital one.
Criminals began plundering open company databases on the Internet. Hackers were drawn to social networking networks, which essentially urged them to develop digital identity theft. The prevalence of viruses, phishing scams, and ransomware increased.
Currently, only the most ignorant individuals leave data unsecured. Security has become a lucrative industry.
According to experts, we will spend $10 billion annually on cybersecurity by 2027.
We’ve collated the main 40 cybersecurity data points for 2023 to offer you a clearer picture of the current level of overall security. This will aid in demonstrating the ubiquity and necessity of cybersecurity in every aspect of an organization. These statistics cover data breaches, hacking statistics, cybercrime types, industry-specific statistics, spending, expenses, and information regarding the cybersecurity job area.
Due to a data breach in 2018, thirty million additional Facebook accounts were exposed. (Facebook)
- According to figures gathered from consumers in 2019, it is anticipated that the number of botnet accounts on social media will see a significant spike. Because of this, it would be impossible to know who to trust, which presents a unique challenge for marketers whose strategies rely on influencer efforts. (McAfee)
- The personal information of around 93 percent of all LinkedIn members was exposed due to a data breach that occurred in 2021 and affected 700 million users. (RestorePrivacy)
- According to statistics on email hacking gathered by Verizon, phishing attempts are responsible for approximately 95% of all espionage attacks. These figures also reveal that phishing attempts are responsible for 80% of all malware infections. (ThreatSim)
- There has been an increase in the amount of spam that appears in the feeds of 47% of social media users. 79% of them are under the impression that spam contains criminal activity and phony news. (Hubspot)
- During a breach that occurred in 2020, 130 Twitter accounts were targeted, including those of former presidents of the United States and Elon Musk, CEO of Tesla. As a consequence, the hackers stole $121,000 in Bitcoin through over 300 separate transactions. (CNBC)
- The statistics on hacking on social media demonstrate that criminals are able to freely discuss their exploits in private groups that are hosted on public platforms. The taking of credit card information is discussed in 53 percent of hacking organizations’ posts on Facebook. There is a mention of account takeovers in 16 percent of all texts. (RSA Security)
- A data breach in the year 2021 caused by incorrectly configured cloud services revealed the personally identifiable information of more than 100 million Android users. (Checkpoint)
- IBM and the Ponemon Institute estimate that the average overall cost of data breaches will have increased by 10% between the years 2020 and 2021. The pandemic of 2020 produced a rise in remote working and digital transformation, which contributed to an increase in the average cost of a data breach of around $1.07 million.
During the pandemic, IBM found that the most common type of data lost was information about customers that could be used to find them. This sort of record was included in around 44% of the breaches, and each record was worth approximately $180.(IBM)
- According to the available data, six out of every ten cyberattacks in the year 2020 were carried out with the intention of extorting money from businesses and individuals. The most well-known data breach occurred at Garmin and cost the corporation 10 million dollars. CTW Global likewise suffered a significant financial loss of $4.5 Million. (Government Technology)
- This is referred to as a data breach when sensitive, confidential, or otherwise protected information is accessed and/or shared without proper authority. According to the “Cost of a Data Breach Report” published by IBM, the typical data breach cost rose by 2.6% from USD 4.24 million in 2021 to USD 4.35 million in 2022. This marks the fourth year in a row in which there has been an annual increase in the average cost. The average price has increased by 12.7% from the 2020 report, which put it at 3.86 million USD. (Cybertalk.org)
- According to the statistics on hacking, hackers attacked five out of six significant organizations with email assaults in the previous year, which is an increase of forty percent from the previous year. (Symantec)
- On average, only around 5 percent of companies’ files have adequate security measures. That suggests that 95% of folders are not password protected. Suppose the contents of your folders contain sensitive information. In that case, it is imperative that it be safeguarded at all times, including while it is being transported and while it is being stored. (Varonis)
- Statistics for the year 2022 reveal that opening attachments in emails with file extensions such as .iso, .exe, .zip, .dmg, and .rar should be avoided at all costs. Be alert for zip and jar files because it is easy for them to circumvent the anti-malware protection offered by most email providers. Files created with Microsoft Office might likewise be a security risk. It’s easy to forget about file extensions like .ppt, .doc, and .xls because the majority of people are already familiar with them. (NordVPN)
- According to research on data breaches that were compiled by IBM in 2022, businesses spent up to $4.24 million on each data breach that occurred in 2021. This is a 10% increase from the total expenditure of $3.86 million in 2019. (Cyber Magazine)
- Up to 45.3% of the emails sent out in December 2021 were considered spam. The remaining emails were marketing-related, although a large majority of them included harmful code. During that time period, the nation of Russia was the source of the greatest amount of unsolicited spam emails. It is estimated that up to 24.7% of the total amount of spam in the world originates from there. (Statista)
- In March of 2022, hackers were able to access about 4 million data. As of the month of March 2022, there have been 88 cybersecurity incidents that were made public. As a direct consequence of this, 3,987,593 records were compromised. The total number of records that were compromised during the first three months of 2022 was 75,099,482. (IT Governance)
- In the year 2022, organizations all around the world will experience a ransomware assault approximately once every 11 seconds. According to statistics on the number of cyberattacks that occur each day, in the year 2022, organizations will fall victim to ransomware assaults almost once every 11 seconds. This is a 20% increase over the previous year, 2019. (Dataprot)
- Eighty-nine percent of healthcare businesses have been victims of data breaches in the previous two years. Cybercriminals target healthcare more than any other sector, making it their top priority. Because it contains important data such as the patient’s complete name, address, health card number, social insurance number, and financial information, patient health information is attractive to cyber hackers. (IDX)
- Human mistake is the cause of 95 percent of all breaches in cybersecurity.
To make it less likely that a data breach will happen because of a breach in cybersecurity, it is important to give employees enough training and the right tools. (Cyberint)
- More than half a million Zoom user accounts were hacked and sold on the underground market. Users of the Zoom platform have become a target for cybercriminals as a result of the platform’s status as the industry standard for video conferencing for businesses. (CPO Magazine)
- Attacks on software supply chains have surged by 650% in recent months. According to a study conducted in 2021, the vast majority of enterprises appear to have been caught off guard. This is supported by the fact that 82% of businesses provide highly privileged responsibilities to third-party suppliers that are a part of their software supply chain. 76% of the accounts had roles that might allow the account to be taken over, and the worst part is that more than 90% of the security teams allocated for the accounts were unaware that such rights were ever granted. (Cybertalks.org)
- According to a prior estimate conducted by CyberSecurity Ventures, there would be one ransomware assault every 11 seconds by 2022. When compared to the projection provided for 2019, which said that there would be 14 attacks per second, this is an increase of almost 20%. (Cybertalk.org)
- Eighty-two percent of the firms that were questioned for the research titled “The State of Incident Response 2021” by VMware are afraid that their business may be subject to a cyber attack. In addition, the survey discovered that 49% of firms do not possess the necessary experience and resources to adequately respond to incidents. (VMware)
- By 2023, thieves will have stolen more than 33 billion records, which is a 175% increase from 2018.
- According to Accenture’s research, 43 percent of cyberattacks target small and medium-sized businesses, yet only 14 percent of those businesses are ready to protect themselves. (Accenture)
- More than half of all customers have been the target of cybercrime, and in the past year alone, almost one-third of all consumers have become victims. (Norton, 2021) (Norton)
- Most individuals (53%) agree that the rise of remote work has made it simpler for hackers and other cybercriminals to take advantage of people. (Norton, 2021) (Norton)
- In 2020, thieves stole a total of $1.9 billion worth of cryptocurrency, which is a decrease from the $4.5 billion they took in 2019. (Finaria, 2021)
- The average amount of ransom paid by organizations of a small size is $170,404. (Source: Sophos, 2021)
- Over the course of the previous five years, the FBI has received over 2.2 million reports of internet-related criminal activity, which resulted in a total of $13.3 billion worth of losses for victims of these crimes. (FBI, 2020)
- On the dark web, a Social Security number may be sold for one dollar, a credit card number would go for up to one hundred ten dollars, and a United States passport might be sold for up to two thousand dollars. (Experian, 2018)
- The number of application-layer distributed denial-of-service attacks directed against the manufacturing industry skyrocketed by a staggering 641% during the fourth quarter of 2021.
- DDoS attacks that target the application layer are intended to take advantage of applications’ weaknesses and render them unable to provide material to users. A record-high number of these attacks were documented during the fourth quarter of 2021, with the manufacturing industry’s primary target of most of them. During this time span, there was a staggering 641% increase in the number of DDoS attacks directed against application layers. ( portswigger.net)
- By 2023, the overall number of DDoS attacks globally will reach 15.4 million. (Cisco)
- The cost of cyber insurance shot up by 96 percent during the third quarter of 2021, representing an increase of 204 percent year-over-year. (Marsh)
- Twenty-two billion records were exposed due to data breaches in 2021. (RiskBased Security)
- The average data breach cost for companies in 2021 was $4.24 million, an increase from $3.86 million the previous year. This was the most it had been in the preceding 17 years. (cybertalk.org)
- Attacks on software supply chains have surged by 650% in recent months. According to a study conducted in 2021, the vast majority of enterprises appear to have been caught off guard. This is supported by the fact that 82% of businesses provide highly privileged responsibilities to third-party suppliers that are a part of their software supply chain. 76% of the accounts had roles that might allow the account to be taken over, and the worst part is that more than 90% of the security teams allocated for the accounts were unaware that such rights were ever granted. (cybertalk.org)
- Compared to the year before, 2021 saw a significant increase in the number of hacking attempts made against commercial entities. The number of weekly hack attacks on corporations grew by 50%. (cybersecurityintelligence.com).
What is a Network Security Trend?
The observation of malicious activities during a given time span, as determined by an analysis of network traffic, is one definition of the term “network security trend.” With the help of these observations, researchers can figure out patterns of attack over time.
Numerous cybersecurity vendors have developed numerous reports on network security trends. The Network Security Trends Report from Palo Alto is an example of such a report.
In Figure, the most common types of vulnerabilities are listed in order of how common they were in the most recent set of vulnerabilities that were made public.
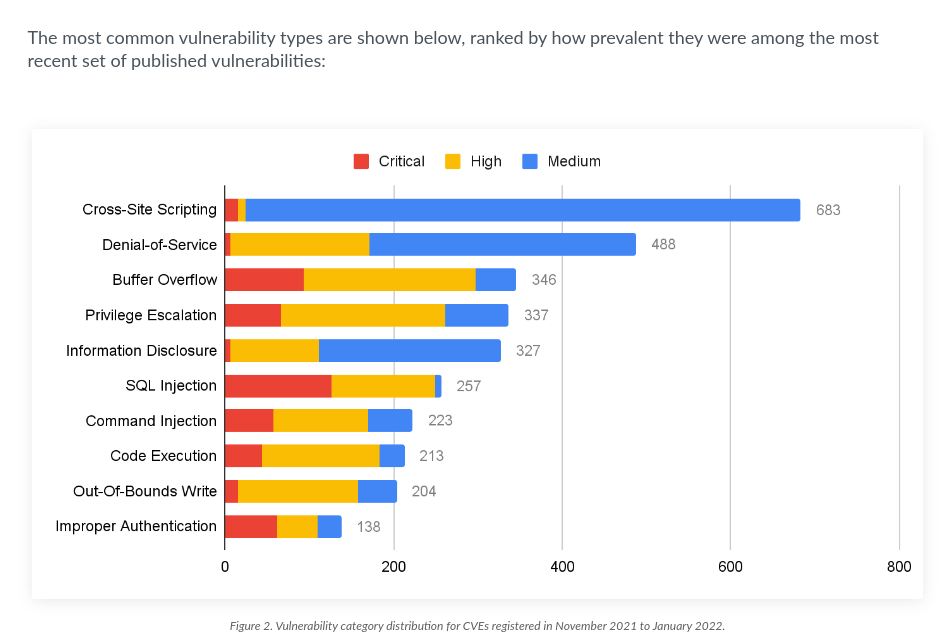
Cross-site scripting is still the vulnerability that gets the most reports from May to July 2022. We also saw that the number of SQL injection vulnerabilities increased during this time, and many of these are rated as critical. The number of SQL injection and cross-site scripting flaws went up a little, but the number of out-of-bound flaws went down. Most of the cross-site scripting and information disclosure attacks that have been reported recently are usually of medium or high severity (rather than critical).
How to Define Hacking?
Hacking can be defined as the act of gaining unauthorized access to information, computer systems, and devices, along with networks. When talking about the definition of the term “hacking.” It is customary to think of it negatively. Even though hacking is unethical in and of itself, there are some forms of it.
As its name indicates, ethical hacking is a type of hacking that is approved by businesses and people in order to locate vulnerabilities and exploit them in a computer system, network, program, or device. Ethical hacking may also be referred to as white hat hacking.
There have been numerous significant hacking incidents throughout history as examples of black hat hacking. One example is the Aramco case.
In July 2021, Saudi Aramco was attacked by hackers after a leak of sensitive information from a third-party contractor. The disclosure was the consequence of a breach in security within the company. The hackers sought a ransom of fifty million dollars after one terabyte of data was exposed to the public. The fact that Saudi Aramco is one of the greatest firms in the world in terms of revenue contributed to the dissemination of this information.
Another case of giant hacking is the Sina Weibo case.
Sina Weibo is one of China’s largest social media networks, with a user base of over 600 million people. In March 2020, the firm made the announcement that an unauthorized third party had stolen a portion of its database. This breach exposed the personal information of 538 million Weibo users, including their actual names, site usernames, gender, location, and phone numbers. After then, it is said that the attacker put the database up for sale on the dark web for a price of $250.
What are the Types of Hacking?
It is helpful to have an understanding of the many attack vectors a malicious actor could utilize in order to inflict harm, whether you are trying to make sense of the newest data breach headline in the news or you are conducting an investigation into an incident that occurred in your own business. An overview of some of the most frequent types of hacking that is observed in today’s world is presented below.
- Phishing
- Virus
- UI redress
- Cookie theft
- Distributed Denial-of-service(DDoS)
- DNS spoofing
- Social Engineering
- Missing Security Patches
- Malware-Injection Devices
- Cracking Password
